Computers and Technology, 21.04.2020 22:13, lennyatme
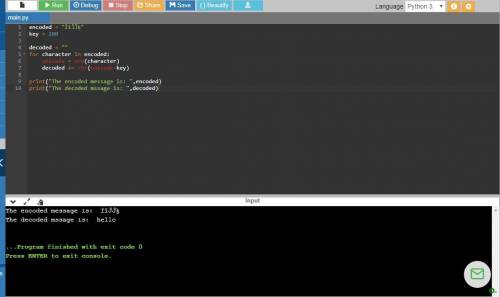
Write a code block to decode strings from secret encodings back to readable messages. To do so: Initialize a variable called decoded as an empty string Use a for loop to loop across all characters of a presumed string variable called encoded Inside the loop, convert the character to another character: Get the unicode code point for the character (using ord) Subtract the value of key to that code point (which should be an int) This undoes the secret encoding of the character, getting back to the original value Convert this new int back to a character (using chr). Also inside the loop, add this converted character to the string decoded

Answers: 3
Other questions on the subject: Computers and Technology

Computers and Technology, 22.06.2019 03:00, nsjcbdhcb
Data is processed, stored, and transmitted as a series of 1s and 0s. each 1 or 0 is called a(n) . a series of eight 0s and 1s, called a(n) , represents one character—a letter, number, or punctuation mark. data becomes when it is presented in a format that people can understand and use. digital signals are represented by two different , such as +5 volts and +.2 volts. digital data can also take the form of light and dark spots etched onto the surface of a cd or the positive and negative orientation of particles on the surface of a hard disk. data consists of numbers that might be used in arithmetic operations. it can be represented digitally using the number system. data is composed of letters, symbols, and numerals that are not used in arithmetic operations. computers represent this type of data using , ebcdic, unicode, or utf-8. data is quantified using terms such as or kibibyte (1024 bytes), and prefixes such as or mebi (1,048,576), and giga or (1,073,741,824). to reduce file size and transmission times, digital data can be compressed. compression provides the means to compress data and reconstitute it into its original state. compression throws away some of the original data during the compression process. compressed files usually have at the end of the file name and are represented with special icons. these files have to be or unzipped before you can view the data they contain.
Answers: 1

Computers and Technology, 22.06.2019 10:40, almaga1979orfvwo
5. illustrate how fine-line inventory classification can be used with product and market segments. what are the benefits and considerations when classifying inventory by product, market, and product/market?
Answers: 2

Computers and Technology, 22.06.2019 14:20, babyrocks7300
Consider a byte-addressable computer with 16mb of main memory, a cache capable of storing a total of 64kb of data and block size of 32 bytes. (a) how many bits in the memory address? (b) how many blocks are in the cache? (c) specify the format of the memory address, including names and sizes, when the cache is: 1. direct-mapped 2. 4-way set associative 3. fully associative
Answers: 2

Computers and Technology, 22.06.2019 17:40, lazerlemon500
Write a modular program (no classes yet, just from what you learned last year), that allows two players to play a game of tic-tac-toe. use a two-dimensional char array with 3 rows and 3 columns as the game board. each element of the array should be initialized with an asterisk (*). the program should display the initial board configuration and then start a loop that does the following: allow player 1 to select a location on the board for an x by entering a row and column number. then redisplay the board with an x replacing the * in the chosen location. if there is no winner yet and the board is not yet full, allow player 2 to select a location on the board for an o by entering a row and column number. then redisplay the board with an o replacing the * in the chosen location. the loop should continue until a player has won or a tie has occurred, then display a message indicating who won, or reporting that a tie occurred. player 1 wins when there are three xs in a row, a column, or a diagonal on the game board. player 2 wins when there are three ox in a row, a column, or a diagonal on the game board. a tie occurs when all of the locations on the board are full, but there is no winner. input validation: only allow legal moves to be entered. the row must be 1, 2, or 3. the column must be 1, 2 3. the (row, column) position entered must currently be empty (i. e., still have an asterisk in it).
Answers: 1
Do you know the correct answer?
Write a code block to decode strings from secret encodings back to readable messages. To do so: Init...
Questions in other subjects:



Mathematics, 11.09.2019 06:10


Business, 11.09.2019 06:10

Business, 11.09.2019 06:10


Business, 11.09.2019 06:10