
Computers and Technology, 03.12.2021 01:40, amyre
Part B
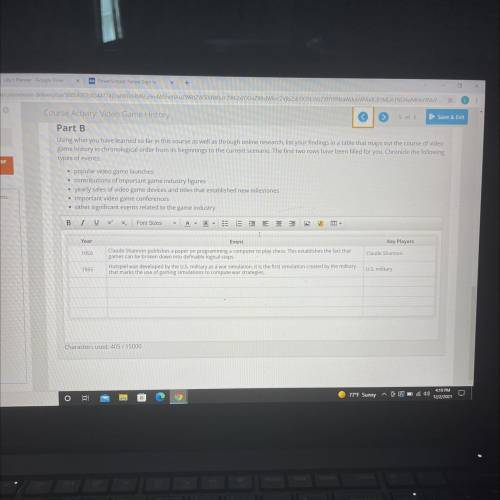
Using what you have learned so far in this course as well as through online research, list your findings in a table that maps out the course of video
game history in chronological order from its beginnings to the current scenario. The first two rows have been filled for you. Chronicle the following
types of events:
• popular video game launches
• contributions of important game industry figures
• yearly sales of video game devices and titles that established new milestones
• important video game conferences
• other significant events related to the game industry

Answers: 3
Other questions on the subject: Computers and Technology

Computers and Technology, 24.06.2019 00:00, miguelturner
Which tool could be used to display only rows containing presidents who served two terms
Answers: 3

Computers and Technology, 24.06.2019 02:30, journeyhile5
How to apply the fly in effect to objects on a slide
Answers: 1

Computers and Technology, 24.06.2019 14:00, ratpizza
Which describes careers that have similar education requirements but different qualifications? product safety engineers and materials engineers industrial safety engineers and industrial health engineers quality control systems managers and inspectors industrial safety and health engineers and hand packers
Answers: 3

Computers and Technology, 24.06.2019 15:20, 710jonathan
Local area networks use many of the same network technologies and the internet, only on a smaller scale. devices that access lans are equipped with a network interface that contains circuitry for wireless or wired connections. devices also have a physical address, in addition to the ip addresses acquired from a dhcp server. the most popular wired technology is . the most popular wireless technology is , which can be configured as a(n) or star topology. setting up a lan and configuring its router is fairly easy. the first step is to change the standard to one that is secure. next, create a(n) that uniquely identifies the network by name. it is also important to activate wireless to prevent wireless signals from being intercepted during transmission. a limited-access network can be created for visitors to use. by activating , the router will be able to assign ip addresses to each device that joins the network. to connect to a secure lan that is protected by encryption, an encryption , or password, is required. lans can be used to access data collected by iot devices and the networks that tie these devices together. technologies such as rfid, nfc, bluetooth smart, zigbee, and z-wave offer -power links, essential for battery-powered devices that can’t expend excess amounts of energy transmitting data.
Answers: 1
Do you know the correct answer?
Part B
Using what you have learned so far in this course as well as through online research, list...
Questions in other subjects:




English, 19.12.2019 20:31











