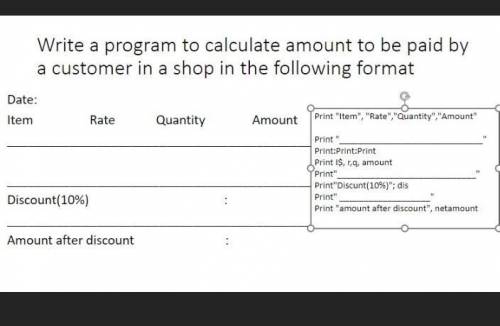
First one sending me the answer will be marked as brainliast.
...

Computers and Technology, 28.08.2021 14:00, karlaperez6852
First one sending me the answer will be marked as brainliast.

Answers: 1
Other questions on the subject: Computers and Technology

Computers and Technology, 24.06.2019 18:20, mshepherdmiller
Acommon algorithm for converting a decimal number to binary is to repeatedly divide the decimal number by 2 and save the remainder. this division is continued until the result is zero. then, each of the remainders that have been saved are used to construct the binary number. write a recursive java method that implements this algorithm. it will accept a value of int and return a string with the appropriate binary character representation of the decimal number. my code: public class lab16{public string converttobinary(int input){int a; if(input > 0){a = input % 2; return (converttobinary(input / 2) + "" +a); } return ""; } }
Answers: 1


Computers and Technology, 25.06.2019 01:30, christyr2002
Once a vulnerability has been identified by nessus, where would you check for more information regarding the identified vulnerability, exploits, and any risk mitigation solution?
Answers: 1

Computers and Technology, 25.06.2019 03:00, reearamrup27
Match the categories in the first column with examples in the second column. 1. good for watching movies 2. maximum power with small size 3. older style mobile devices that may or may not have internet connectivity tablet computer a.)pda b.)smart phone c.)tablet computer
Answers: 1
Do you know the correct answer?
Questions in other subjects:

Biology, 09.11.2020 21:00


Mathematics, 09.11.2020 21:00

Engineering, 09.11.2020 21:00



Mathematics, 09.11.2020 21:00

Mathematics, 09.11.2020 21:00

Social Studies, 09.11.2020 21:00






