
Computers and Technology, 22.04.2021 17:40, zahriamarie10
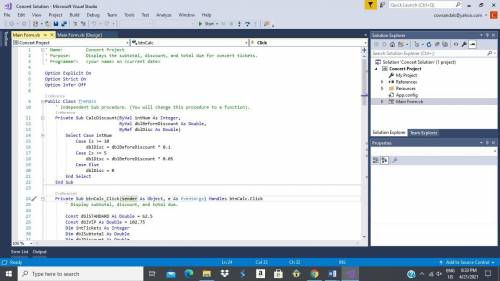
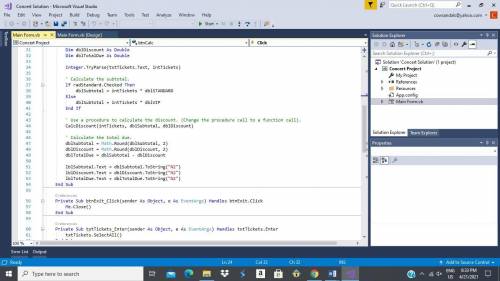
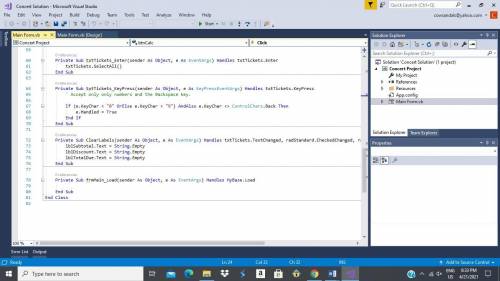
Microsoft Visual Basic Studio Programming
1. Change the CalcDiscount procedure to a function.
2. Make the necessary modifications to the bntCalc_Click procedure.

Answers: 2
Other questions on the subject: Computers and Technology

Computers and Technology, 22.06.2019 01:50, divine134
A.) generate scaffolding to create database for your application. develop all the entities identified in assignment #2. add any additional that may be identified later. b.) add data validation rules to the models that are appropriate for your application and data. c.) create links for each scaffold in the header section. part 2: application updates [30 points] a.) add two additional views to the "home" controller you created in assignment #1. b.) the two views should be named as “privacy" and "". c.) link the two newly created views in the footer section. hint: you would need to modify the “home" controller definition and create “privacy. html. erb" and “.html. erb" files in appropriate locations.
Answers: 3

Computers and Technology, 22.06.2019 12:50, michaelchavez6959127
You have just been hired as an information security engineer for a large, multi-international corporation. unfortunately, your company has suffered multiple security breaches that have threatened customers' trust in the fact that their confidential data and financial assets are private and secured. credit-card information was compromised by an attack that infiltrated the network through a vulnerable wireless connection within the organization. the other breach was an inside job where personal data was stolen because of weak access-control policies within the organization that allowed an unauthorized individual access to valuable data. your job is to develop a risk-management policy that addresses the two security breaches and how to mitigate these risks. requirementswrite a brief description of the case study. it requires two to three pages, based upon the apa style of writing. use transition words; a thesis statement; an introduction, body, and conclusion; and a reference page with at least two references. use a double-spaced, arial font, size 12.
Answers: 1

Computers and Technology, 22.06.2019 13:30, baeethtsadia
Asoftware company hired ray, a college graduate to work in their development team. ray is assigned to work in the coding phase of a project. what happens during the coding phase of a software development project? a. the customer receives a working model of the software. b. developers convert the program design into code. c. developers gather requirements directly from the stakeholders. d. testing teams check the product for quality.
Answers: 1

Computers and Technology, 23.06.2019 00:20, kathlynskare06
Ihave been given the number of guns per 100, and the total firearm-related deaths per 100,000. i have to find the actual number of guns per country and actual number of gun-related deaths. if somebody could show me how to do 1 question, i can finish the rest, i am just confused. tia
Answers: 3
Do you know the correct answer?
Microsoft Visual Basic Studio Programming
1. Change the CalcDiscount procedure to a function.
Questions in other subjects:



Mathematics, 18.02.2020 16:24



Health, 18.02.2020 16:25

Mathematics, 18.02.2020 16:25








