Computers and Technology, 05.02.2020 09:56, romanlittlewood
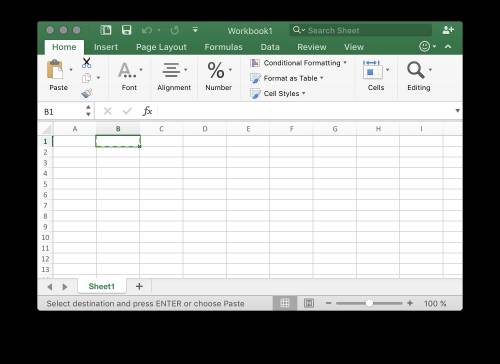
When you select cells in your worksheet and then click the copy button, what happens? select one: a. the formatting is removed from the cells. b. the contents are cleared from the cells. c. the cells are erased. d. a moving dashed line border appears around the cells.

Answers: 3
Other questions on the subject: Computers and Technology

Computers and Technology, 22.06.2019 00:30, huntbuck14
Which of the following methods could be considered a “best practice” in terms of informing respondents how their answers to an on-line survey about personal information will be protected? respondents are informed that investigators will try to keep their participation confidential; however, confidentiality cannot be assured. respondents are informed that a research assistant will transfer all the research data to a password-protected computer that is not connected to the internet, via a usb flashdrive. the computer is located in a research team member’s office. the investigator uses the informed consent process to explain her institution’s method for guaranteeing absolute confidentiality of research data. the investigator uses the informed consent process to explain how respondent data will be transmitted from the website to his encrypted database without ever recording respondents’ ip addresses, but explains that on the internet confidentiality cannot be absolutely guaranteed.
Answers: 1

Computers and Technology, 23.06.2019 11:00, shawn20034
This chapter lists many ways in which becoming computer literate is beneficial. think about what your life will be like once you’re started in your career. what areas of computing will be most important for you to understand? how would an understanding of computer hardware and software you in working from home, working with groups in other countries and contributing your talents.
Answers: 1

Computers and Technology, 23.06.2019 14:30, naomi20044
Select the correct answer. andy received a potentially infected email that was advertising products. andy is at risk of which type of security threat? a. spoofing b. sniffing c. spamming d. phishing e. typo-squatting
Answers: 2

Computers and Technology, 23.06.2019 21:50, Trinhphuongtran
Description: write function lastfirst() that takes one argument—a list of strings of the format "lastname, firstname" —and returns a list consisting of two lists: (a) a list of all the last names (b) a list of all the first names
Answers: 2
Do you know the correct answer?
When you select cells in your worksheet and then click the copy button, what happens? select one:...
Questions in other subjects:

Mathematics, 26.03.2020 23:41

Chemistry, 26.03.2020 23:41




Mathematics, 26.03.2020 23:41




Health, 26.03.2020 23:41