And of course I'll make you as Branlist
...

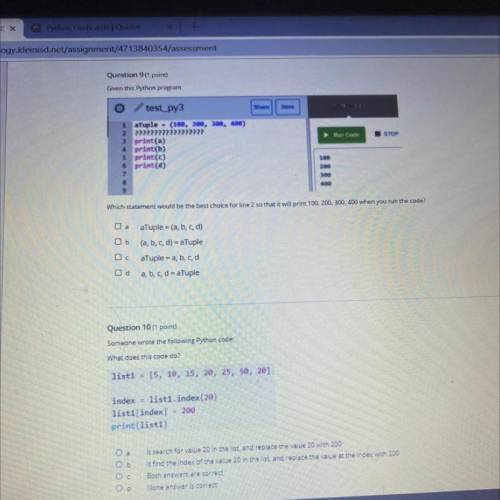
Answers: 2
Other questions on the subject: Computers and Technology

Computers and Technology, 23.06.2019 14:30, naomi20044
Select the correct answer. andy received a potentially infected email that was advertising products. andy is at risk of which type of security threat? a. spoofing b. sniffing c. spamming d. phishing e. typo-squatting
Answers: 2

Computers and Technology, 24.06.2019 19:00, taridunkley724
Which of the following "invisible" marks represents an inserted tab?
Answers: 1

Computers and Technology, 24.06.2019 22:10, jsjsjsskakwkowwj
Function name: poly parameters: int returns: int description: a polynomial of degree n with coefficients a0,a1,a2,a3, . . ,an is the function p(x) = a0+a1x+a2x2+a3 ∗ x3+ . . +an ∗ xn this function can be evaluated at different values of x. for example, if: p(x) = 1+2x+ x2, then p(2) = 1+2 ∗ 2+22 = 9. if p(x) = 1+x2+x4, then p(2) = 21 and p(3) = 91. write a function poly() that takes as input a list of coefficients a0, a1, a2, a3, . . , an of a polynomial p(x) and a value x. the function will return poly(x), which is the value of the polynomial when evaluated at x.
Answers: 3

Computers and Technology, 25.06.2019 01:30, parislover2000
What controls can be found on the file tab of microsoft word
Answers: 1
Do you know the correct answer?
Questions in other subjects:

History, 09.04.2020 20:29









History, 09.04.2020 20:29