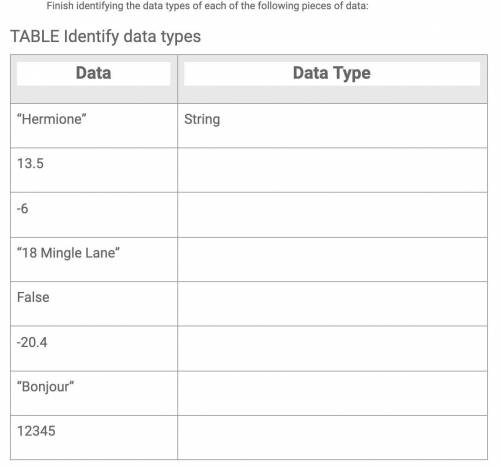
HELP! Finish identifying the data types of each of the following pieces of data:
...

Computers and Technology, 17.11.2020 01:50, pedrojulianhdz2005
HELP! Finish identifying the data types of each of the following pieces of data:

Answers: 2
Other questions on the subject: Computers and Technology

Computers and Technology, 22.06.2019 17:40, lazerlemon500
Write a modular program (no classes yet, just from what you learned last year), that allows two players to play a game of tic-tac-toe. use a two-dimensional char array with 3 rows and 3 columns as the game board. each element of the array should be initialized with an asterisk (*). the program should display the initial board configuration and then start a loop that does the following: allow player 1 to select a location on the board for an x by entering a row and column number. then redisplay the board with an x replacing the * in the chosen location. if there is no winner yet and the board is not yet full, allow player 2 to select a location on the board for an o by entering a row and column number. then redisplay the board with an o replacing the * in the chosen location. the loop should continue until a player has won or a tie has occurred, then display a message indicating who won, or reporting that a tie occurred. player 1 wins when there are three xs in a row, a column, or a diagonal on the game board. player 2 wins when there are three ox in a row, a column, or a diagonal on the game board. a tie occurs when all of the locations on the board are full, but there is no winner. input validation: only allow legal moves to be entered. the row must be 1, 2, or 3. the column must be 1, 2 3. the (row, column) position entered must currently be empty (i. e., still have an asterisk in it).
Answers: 1

Computers and Technology, 22.06.2019 18:30, cascyrio2002
What is outfitting a workplace with video in a technology
Answers: 2

Computers and Technology, 23.06.2019 14:00, savannnab1890
Select the correct answer. andre was recently hired by an organization to check for system vulnerabilities. he is supposed to exploit these vulnerabilities and create a report on the extent of damage to which the system was susceptible. what position does andre hold in this organization? a. information security analyst b. information assurance manager c. penetration tester d. network security engineer e. chief information security officer
Answers: 2

Computers and Technology, 23.06.2019 22:20, andrew412603
Learning sign language is an example of a(n) learning sign language is an example of a(n)
Answers: 2
Do you know the correct answer?
Questions in other subjects:

Biology, 21.11.2020 09:00


English, 21.11.2020 09:00

Mathematics, 21.11.2020 09:00


SAT, 21.11.2020 09:00

English, 21.11.2020 09:00

English, 21.11.2020 09:00

Chemistry, 21.11.2020 09:00

Mathematics, 21.11.2020 09:00






