Computers and Technology, 06.04.2020 23:20, mimithurmond03
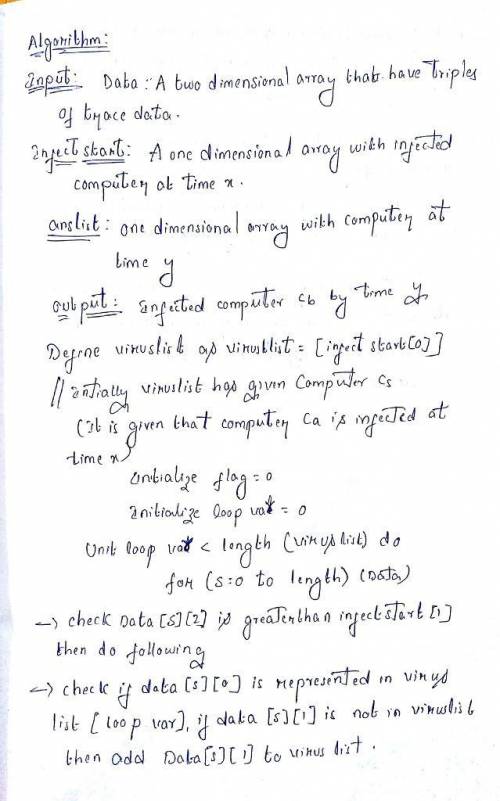
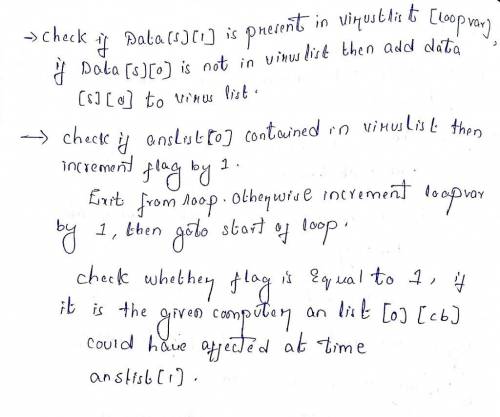
Design an algorithm that answers questions of this type: given a collection of trace data, the algorithm should decide whether the fake information generated by com- puter Ca at time x could have been received by computer Cb by time y. The algorithm should run in time O(m n).

Answers: 1
Other questions on the subject: Computers and Technology

Computers and Technology, 22.06.2019 15:30, alexdub9649
What is a costume plot? why is it important to a film or theater production?
Answers: 2



Computers and Technology, 23.06.2019 11:30, leapfroggiez
Auser is given read permission to a file stored on an ntfs-formatted volume. the file is then copied to a folder on the same ntfs-formatted volume where the user has been given full control permission for that folder. when the user logs on to the computer holding the file and accesses its new location via a drive letter, what is the user's effective permission to the file? a. read b. full control c. no access d. modify e. none of the above
Answers: 1
Do you know the correct answer?
Design an algorithm that answers questions of this type: given a collection of trace data, the algor...
Questions in other subjects:





Mathematics, 31.03.2021 01:20


Mathematics, 31.03.2021 01:20



Mathematics, 31.03.2021 01:20