Computers and Technology, 30.03.2020 22:34, kcarstensen59070
You decide to begin your presentation by providing your audience an overview of networking, with an emphasis on security and why it is important for all company roles to assist in securing the company’s network. You decide to use the OSI model to explain the fundamental characteristics and components of networks because it is visual and presents the complexity of network communication in just 7 steps.
Include a discussion of each of the following in your response, being sure to emphasize the point(s) in the seven-layer OSI model where security is an issue, and listing specific security risks associated with each pain point:
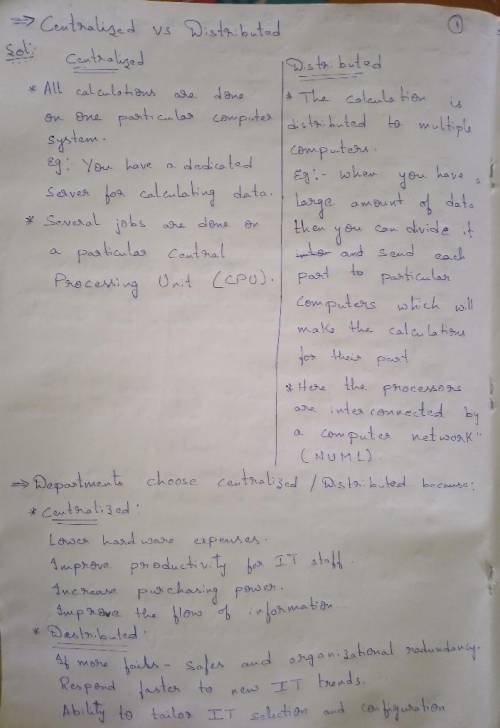
Distributed vs. centralized computer systems and why your department chose to be distributed/centralized
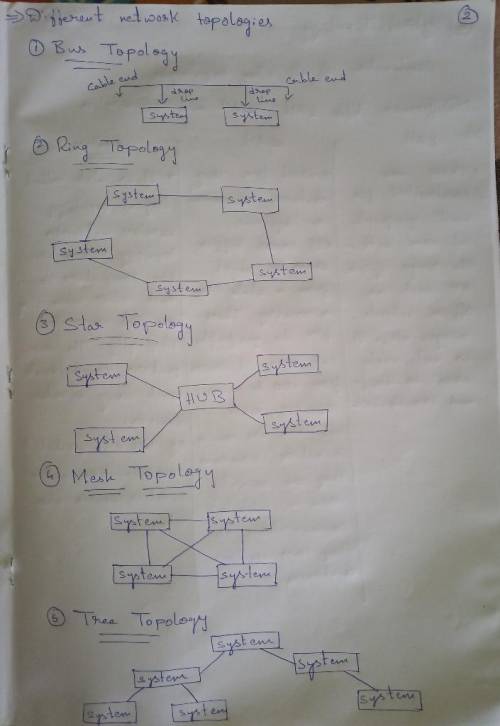
Different network topologies and why your department chose the topology it did
Why standards bodies are essential in networking and how your department complies with standards
The importance of communication protocols and which one(s) your department chose
The differences between LAN, WAN, and wireless technologies, and how your department incorporated each
The responsibilities associated with providing telecommunications services such as security, privacy, reliability, and performance
Next, you plan to describe basic routing and switching in the context of the OSI model (i. e., in which layer routing, switching, and cabling occur). To underscore your department’s commitment to achieving 24/7 availability, you describe some strategies your department follows to ensure the availability of network access in switched and routed networks.
Then, you describe at least three characteristics of an effective security policy, emphasizing the ways in which all departments in the company are responsible for helping secure the company network.
To reassure your audience of your network’s security, you list some strategies your department used to build security directly into the design of your company network.
Finally, malware has been in the news a lot lately, and you know you will be asked some questions about it. To answer them, you come up with a layperson-friendly definition of malware and identify at least two strategies your department has put into place for protecting your company’s network against malware.

Answers: 3
Other questions on the subject: Computers and Technology

Computers and Technology, 22.06.2019 12:20, crodriguez87
Usually, when we sniff packets, we are only interested certain types of packets. we can do that by setting filters in sniffing. scapy’s filter use the bpf (berkeley packet filter) syntax; you can find the bpf manual from the internet. set the following filters and demonstrate your sniffer program again (each filter should be set separately): (a) capture only the icmp packet. (b) capture any tcp packet that comes from a particular ip and with a destination port number 23. (c) capture packets comes from or to go to a particular subnet. you can pick any subnet, such as 128.230.0.0/16; you should not pick the subnet that your vm is attached to.
Answers: 3

Computers and Technology, 23.06.2019 01:10, kristofwr3444
Are special combinations of keys that tell a computer to perform a command. keypads multi-keys combinations shortcuts
Answers: 1


Computers and Technology, 24.06.2019 12:50, opgbadwolf5
When is it most apprpriate for a development team to change the definition of done
Answers: 1
Do you know the correct answer?
You decide to begin your presentation by providing your audience an overview of networking, with an...
Questions in other subjects: