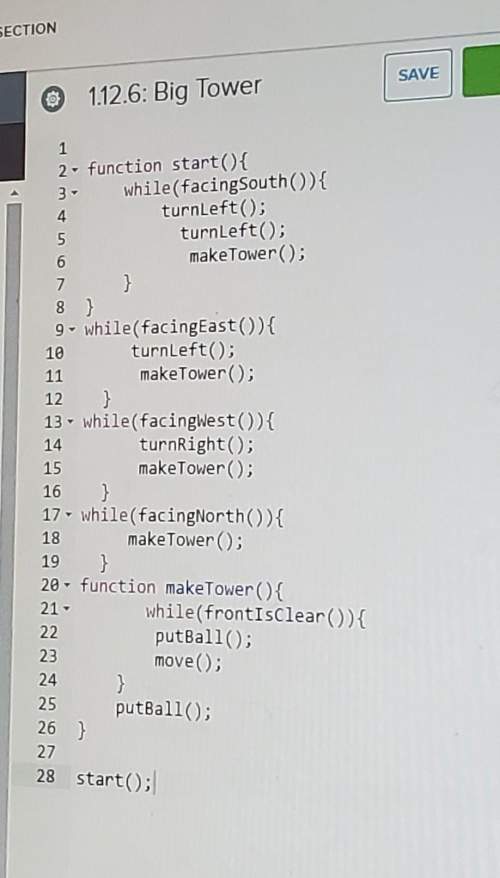
How do you do this code its on codehs (with karel) its the internet technologies class
...

Computers and Technology, 22.11.2019 00:31, kkmoney87
How do you do this code its on codehs (with karel) its the internet technologies class

Answers: 3
Other questions on the subject: Computers and Technology

Computers and Technology, 22.06.2019 10:40, Morghurley2000
"it security policy enforcement and monitoring" respond to the following: describe how monitoring worker activities can increase the security within organizations. describe the rationale that managers should use to determine the degree of monitoring that the organization should conduct. explain the extent to which you believe an organization has the right to monitor user actions and traffic. determine the actions organizations can take to mitigate the potential issues associated with monitoring user actions and traffic.
Answers: 3

Computers and Technology, 23.06.2019 01:10, kristofwr3444
Are special combinations of keys that tell a computer to perform a command. keypads multi-keys combinations shortcuts
Answers: 1

Computers and Technology, 23.06.2019 10:50, whyidkmyself
Your friend kayla is starting her own business and asks you whether she should set it up as a p2p network or as a client-server network. list three questions you might ask to kayla decide which network to use and how her answers to those questions would affect your recommendation.
Answers: 2

Computers and Technology, 23.06.2019 23:30, yasarhan2
Match the following errors with their definitions. a. #name b. #value c. #ref d. 1. when a formula produces output that is too lengthy to fit in the spreadsheet cell 2. when you enter an invalid cell reference in a formula 3. when you type text in cells that accept numeric data 4. when you type in a cell reference that doesn’t exist
Answers: 1
Do you know the correct answer?
Questions in other subjects:

Mathematics, 27.09.2019 21:00














