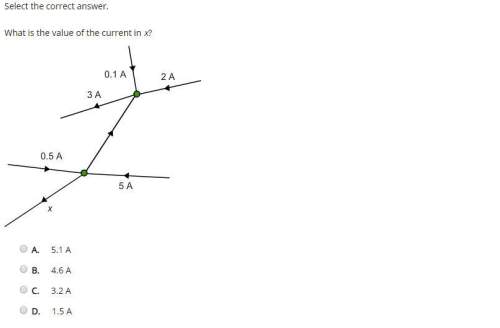
What is the value of the current in x?
...

Answers: 2
Other questions on the subject: Computers and Technology

Computers and Technology, 21.06.2019 14:20, ashl3yisbored
The concept of comes from the acknowledgment that data changes form and often gets copied, moved, and stored in many places. sensitive data often leaves the protection of application databases and ends up in e-mails, spreadsheets, and personal workstation files.
Answers: 3

Computers and Technology, 22.06.2019 14:50, williamsgregg5214
Drag each label to the correct location on the image list the do’s and don’ts of safeguarding your password. a. keep yourself logged in when you leave your computer. b. don’t write your password down and leave it where others can find it. c. share your password with your friends. d.each time you visit a website, retain the cookies on your computer. e. use a long password with mixed characters.1. do's 2. don'ts
Answers: 2

Computers and Technology, 22.06.2019 22:30, reinasuarez964
One of your customers wants you to build a personal server that he can use in his home. one of his concerns is making sure he has at least one backup of their data stored on the server in the event that a disk fails. you have decided to back up his data using raid. since this server is for personal use only, the customer wants to keep costs down. therefore, he would like to keep the number of drives to a minimum. which of the following raid systems would best meet the customer's specifications? a. raid 0 b. raid 1 c. raid 5 d. raid 10
Answers: 3
Do you know the correct answer?
Questions in other subjects:

Physics, 19.01.2021 22:50


Geography, 19.01.2021 22:50





Biology, 19.01.2021 22:50


Spanish, 19.01.2021 22:50